by CPI Staff | Apr 9, 2026 | AI, Blog, Cybersecurity, Entra ID, Microsoft 365 Security
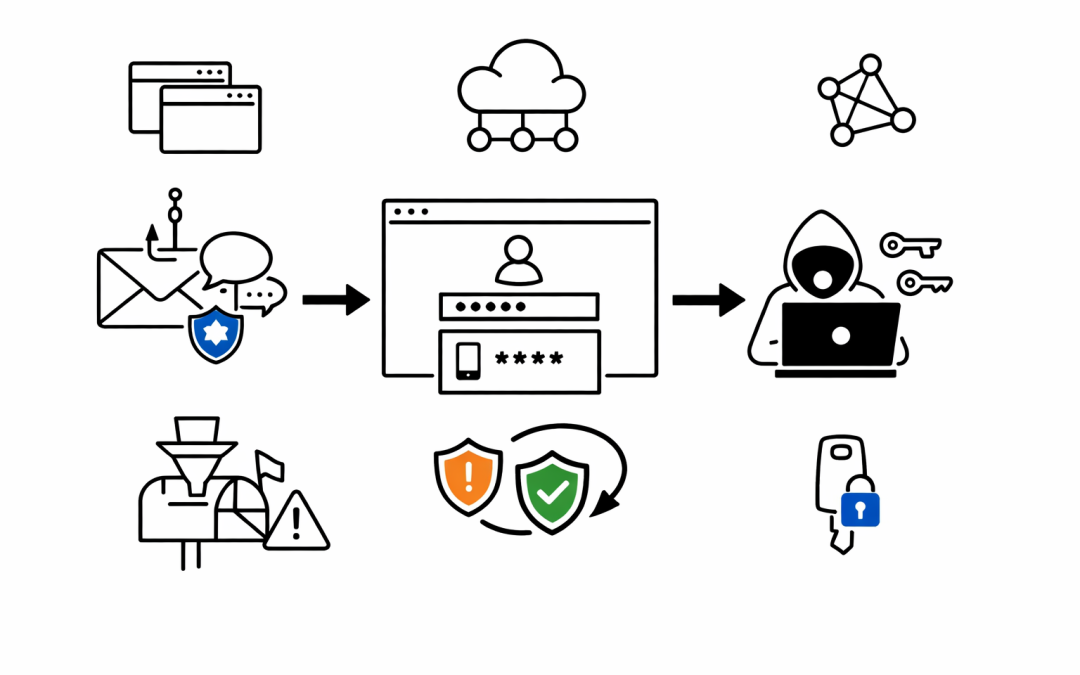
Multi-factor authentication has been the security baseline for years. Most Australian organisations treat it as the final checkpoint — if MFA is in place, accounts are protected. That assumption just got a serious challenge. Microsoft Defender Security Research has...

by CPI Staff | Apr 2, 2026 | Application Development, Blog, Cybersecurity, Essential 8
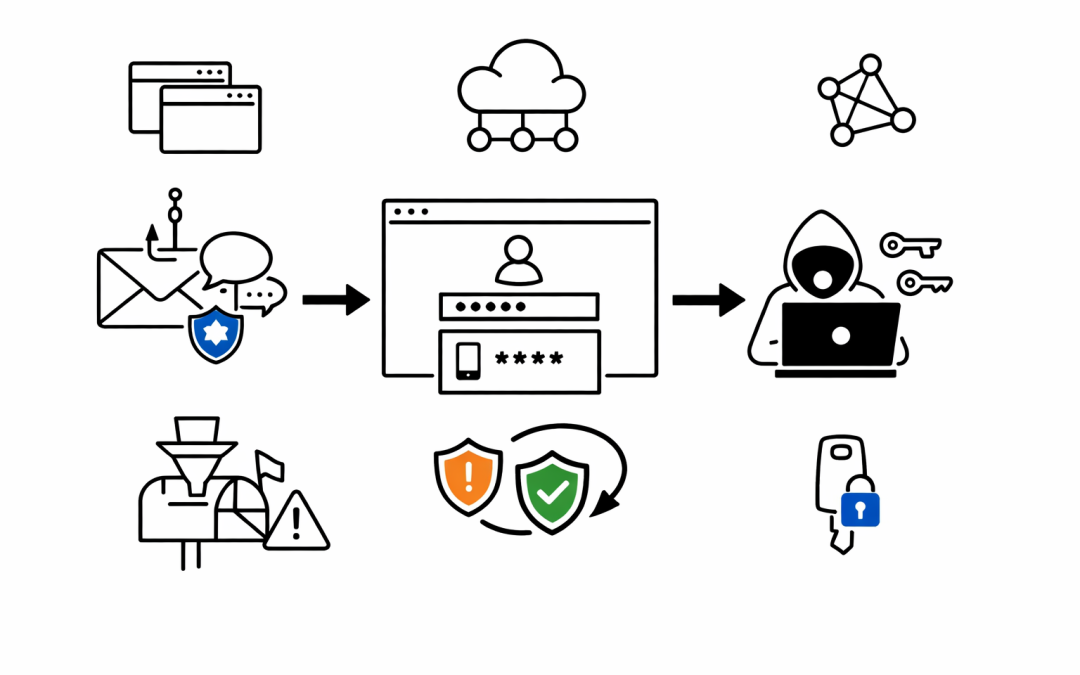
Most organisations still treat dependency management as a developer hygiene issue. The Axios npm compromise shows that assumption is now dangerous. When two malicious Axios versions were published on March 31, 2026, the problem was not limited to a bad package update....

by CPI Staff | Apr 2, 2026 | AI, AI Coding Agents, Anthropic, Blog, Claude Code, Cybersecurity, Essential 8
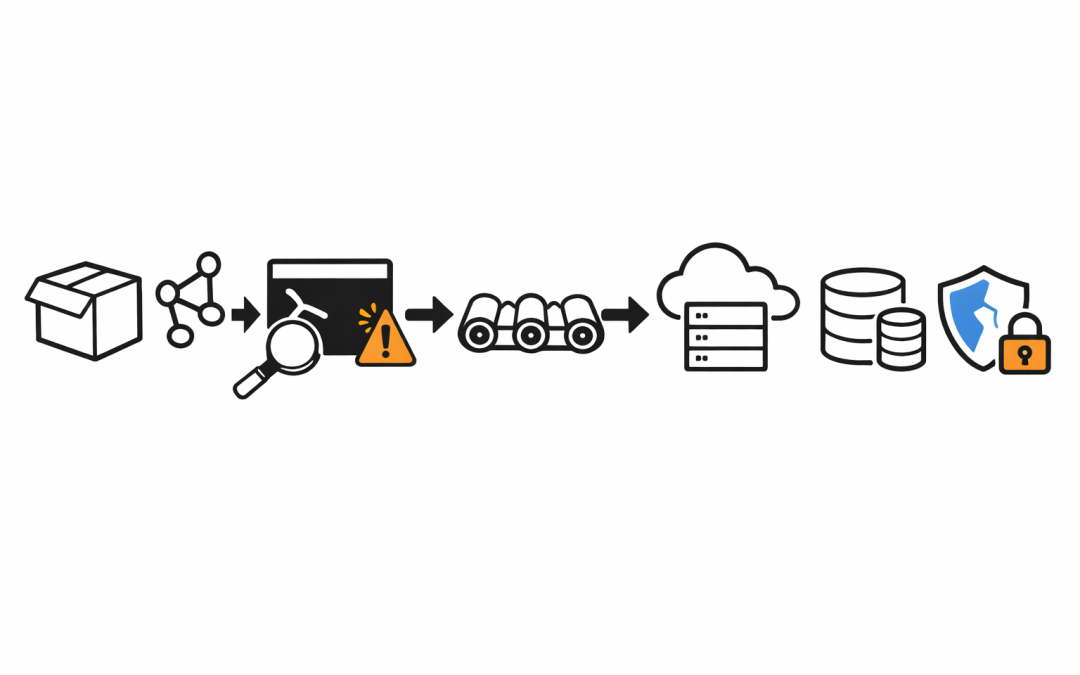
The immediate story was easy to misunderstand. On April 1-2 2026, Anthropic confirmed that a Claude Code release packaging issue was caused by human error, not a security breach. Anthropic also said no customer data or credentials were exposed. That matters. But the...

by CPI Staff | Feb 23, 2026 | AI, Blog, Cybersecurity
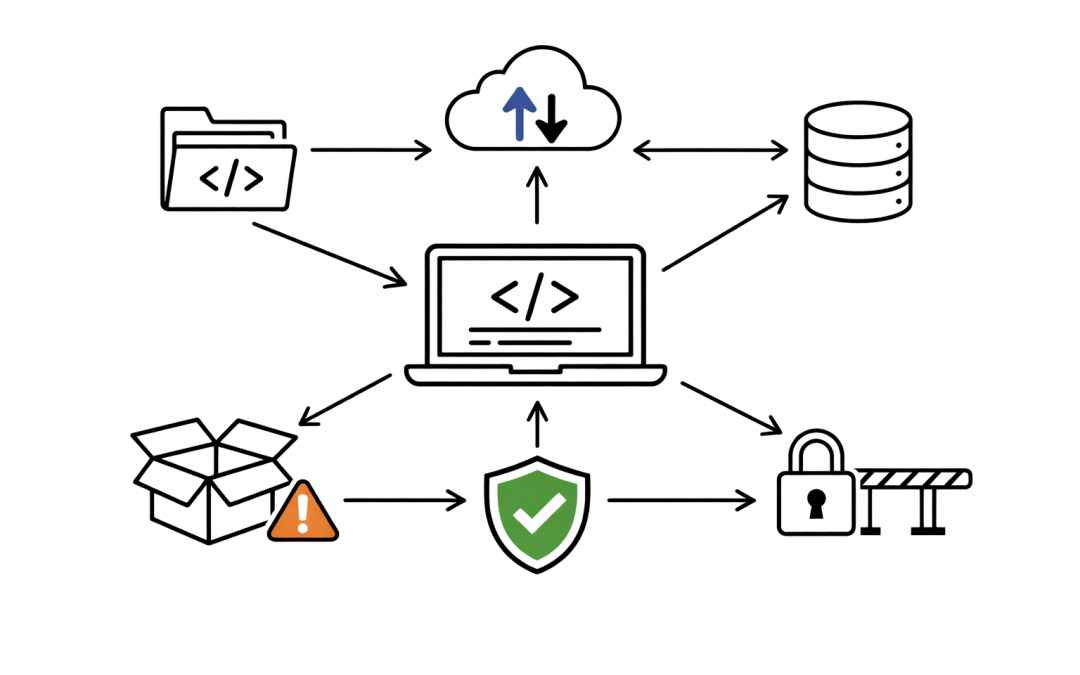
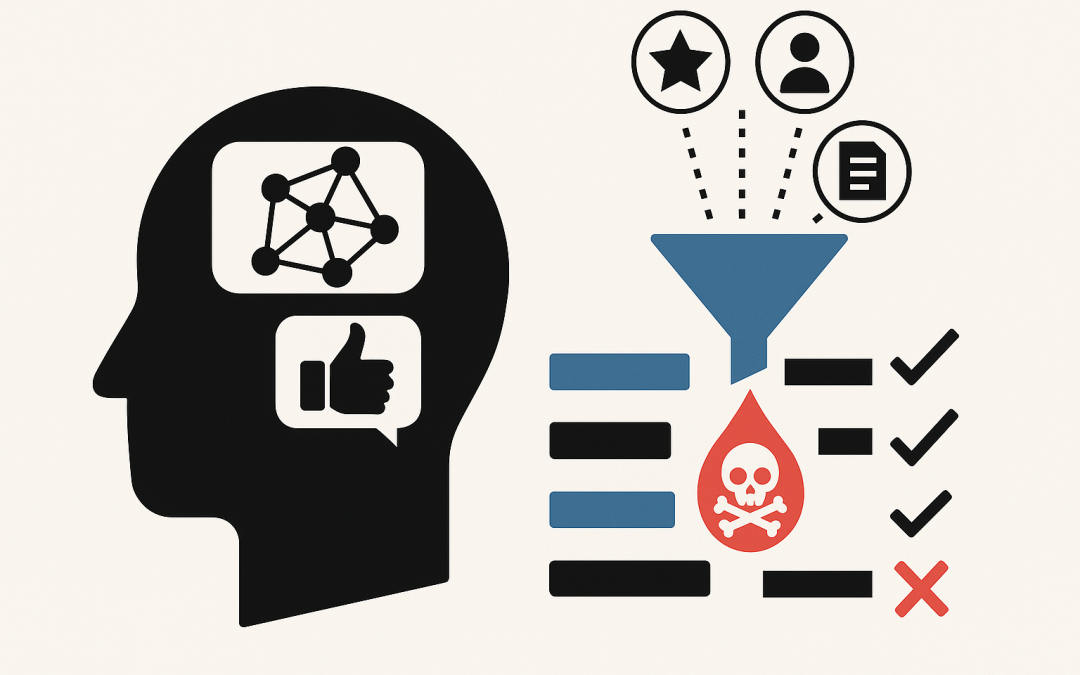
In this blog post AI Recommendation Poisoning How Attackers Skew What Your AI Suggests we will walk through what recommendation poisoning is, why it’s becoming a real-world risk, and what practical steps you can take to reduce the chance your AI gets “nudged” into...