by CPI Staff | Apr 2, 2026 | AI, AI Coding Agents, Anthropic, Blog, Claude Code, Cybersecurity, Essential 8
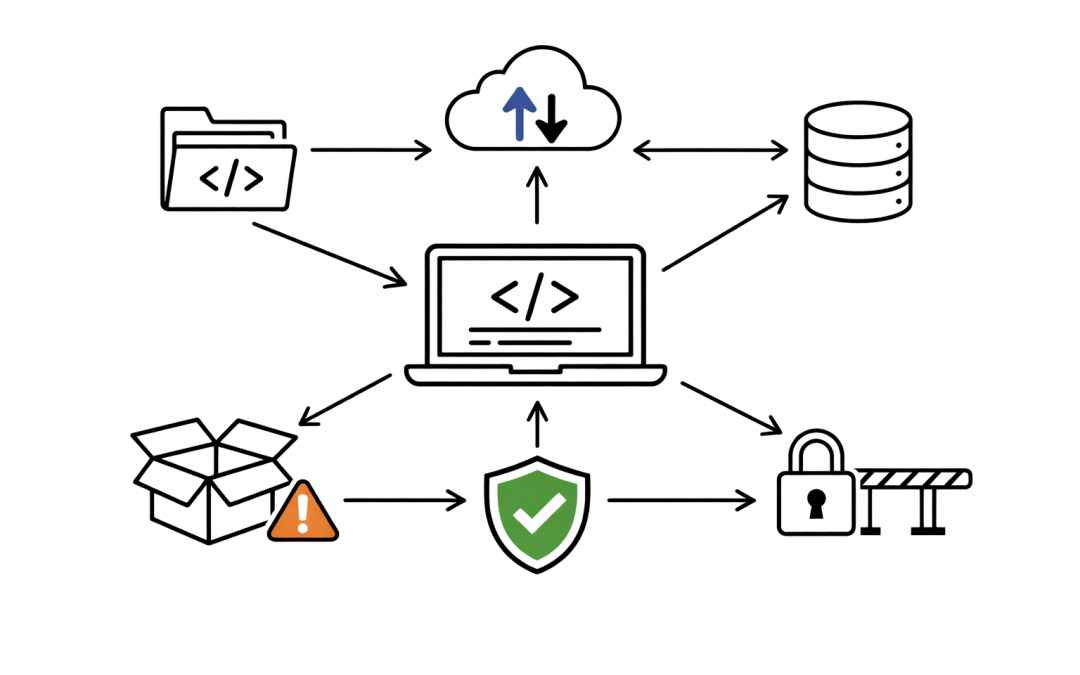
The immediate story was easy to misunderstand. On April 1-2 2026, Anthropic confirmed that a Claude Code release packaging issue was caused by human error, not a security breach. Anthropic also said no customer data or credentials were exposed. That matters. But the...

by CPI Staff | Feb 20, 2026 | Blog, Claude Code
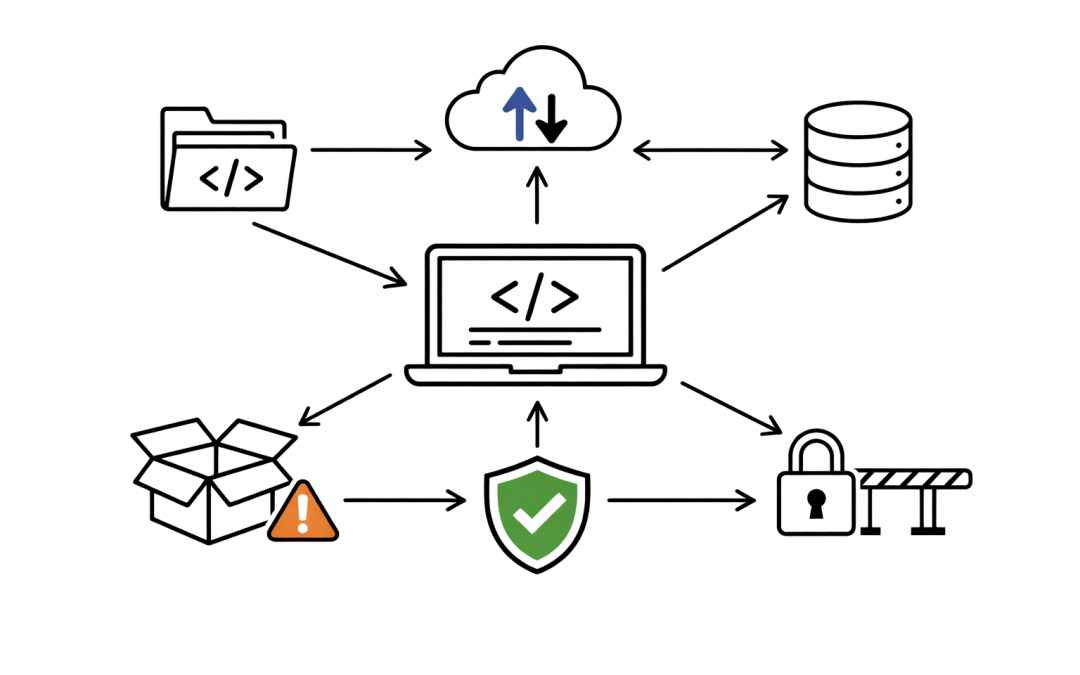
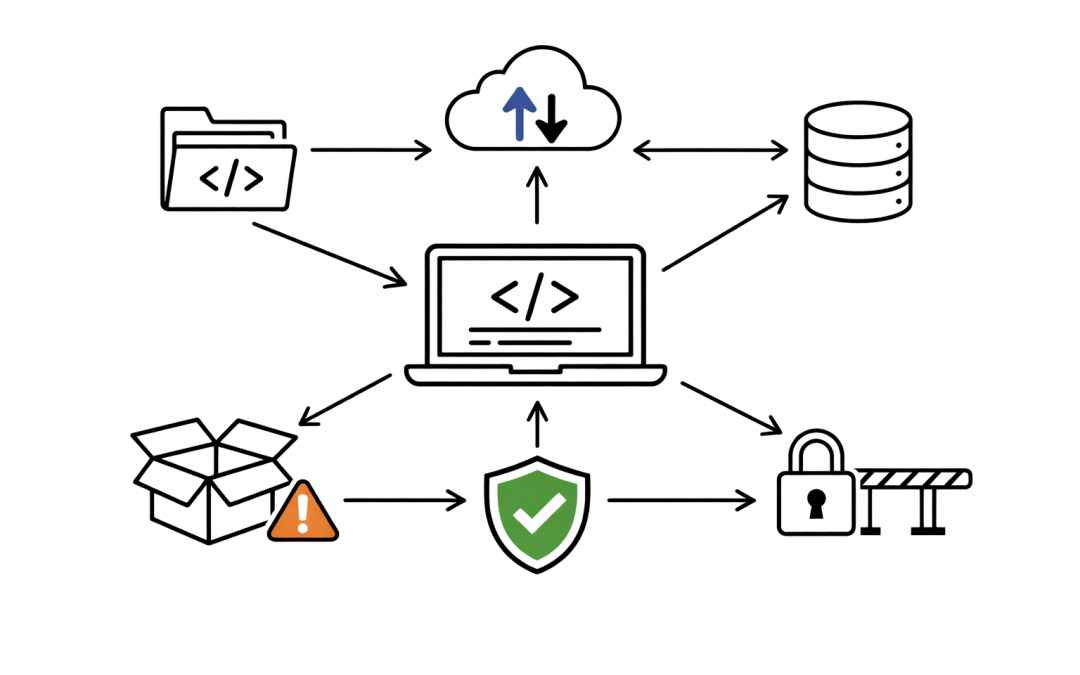
In this blog post Why Claude Code Is Suddenly on Every CIO’s Radar in 2026 we will explain what Claude Code is, why it’s getting so much attention right now, and the practical next steps to adopt it safely and profitably. Why Claude Code Is Suddenly on Every CIO’s...