by CPI Staff | Apr 7, 2026 | AI for Business & AI Strategy, AI Vendor Selection & Implementation, Blog
When a company that did not exist five years ago hits a $30 billion annualised revenue run rate, it is no longer a startup story. It is a market signal. Anthropic’s reported revenue trajectory — growing from roughly $2 billion in annualised revenue in early 2025...

by CPI Staff | Apr 4, 2026 | AI, AI Agents, Blog
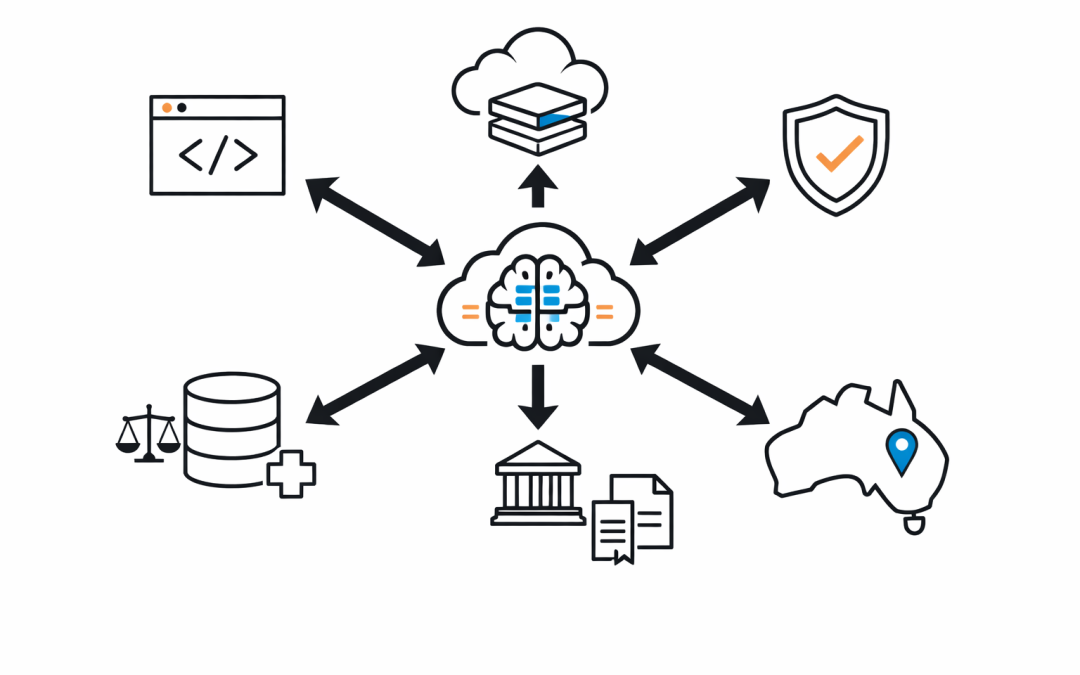
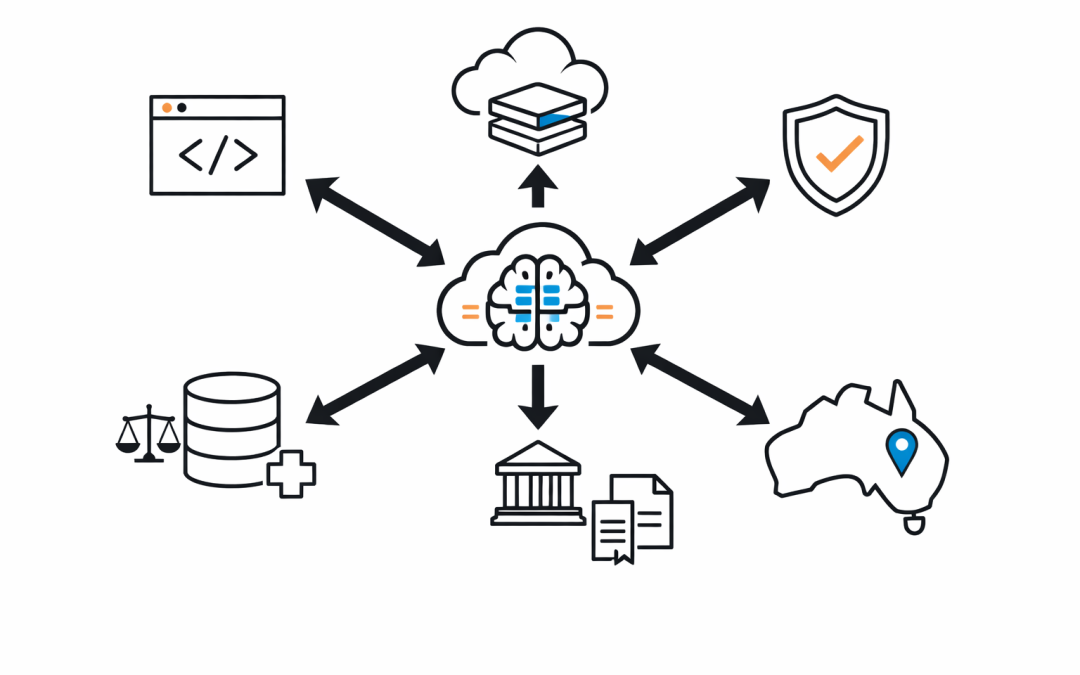
Zero Trust is well understood for users. Verify identity, check device health, enforce least privilege, assume breach. Most mature IT organisations have some version of this in place. AI agents break that model. Not because Zero Trust principles are wrong — but...

by CPI Staff | Apr 3, 2026 | AI, Blog, Google
Google’s Threat Intelligence Group just published one of the most detailed reports to date on how adversaries are using AI to accelerate attacks. For Australian CISOs, five findings demand immediate attention. The GTIG AI Threat Tracker, published in early 2026...

by CPI Staff | Apr 2, 2026 | AI, Blog
The attack surface for mid-market organisations has expanded faster than most security strategies have adapted. AI is not just a tool for defenders. It is now an operational accelerator for attackers — and the techniques are not science fiction. Google’s Threat...

by CPI Staff | Apr 2, 2026 | Application Development, Blog, Cybersecurity, Essential 8
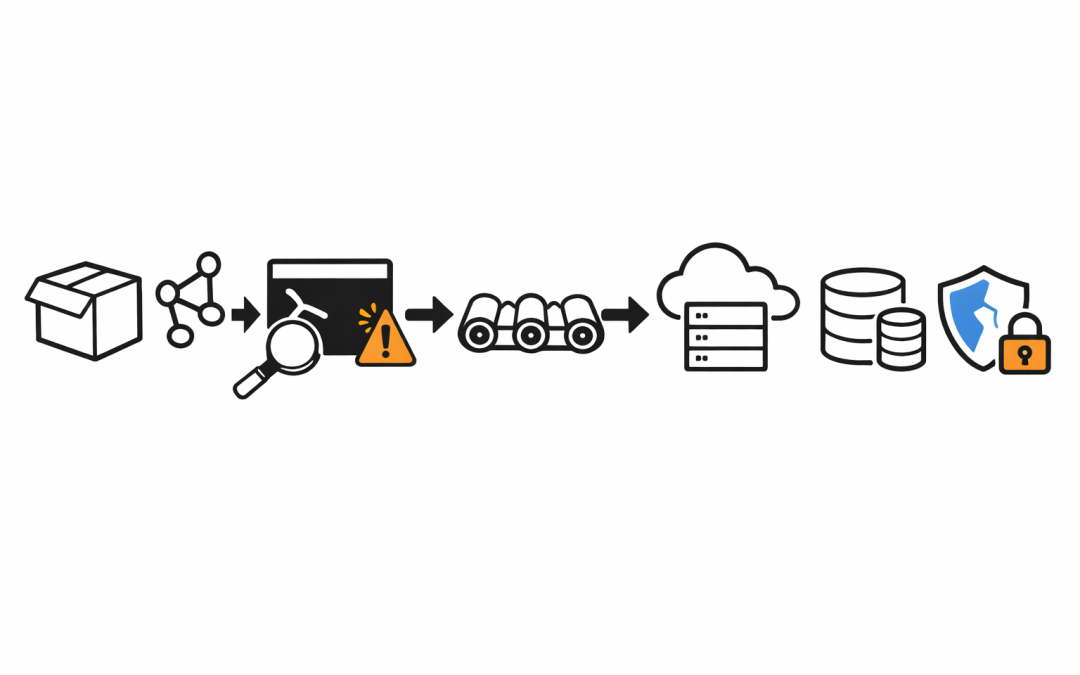
Most organisations still treat dependency management as a developer hygiene issue. The Axios npm compromise shows that assumption is now dangerous. When two malicious Axios versions were published on March 31, 2026, the problem was not limited to a bad package update....

by CPI Staff | Apr 2, 2026 | AI, AI Coding Agents, Anthropic, Blog, Claude Code, Cybersecurity, Essential 8
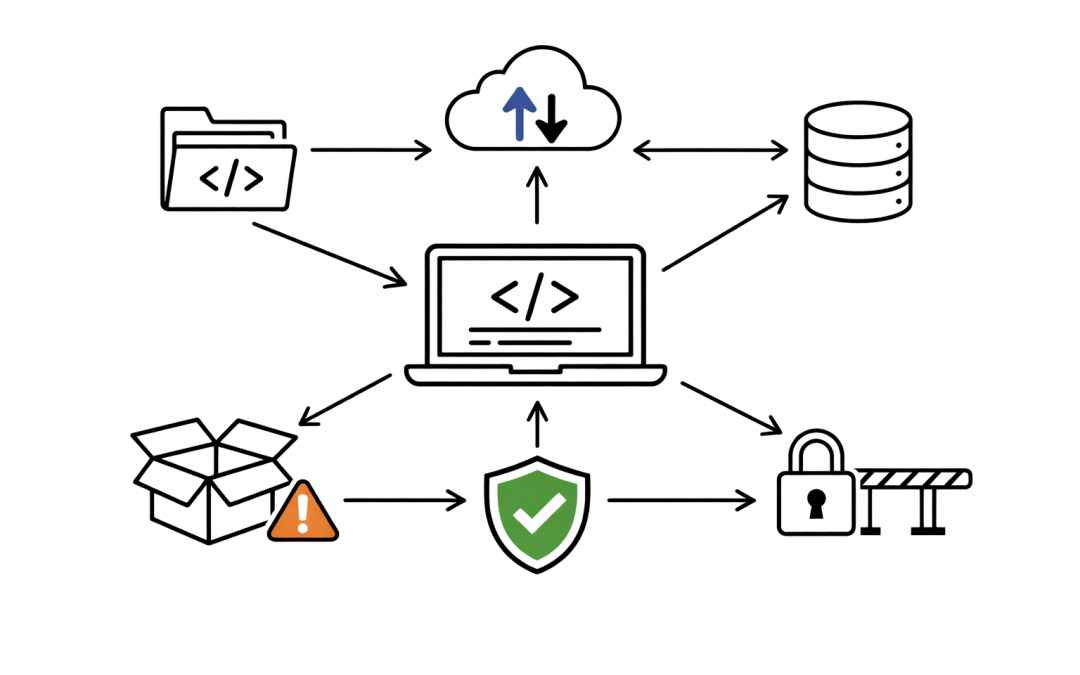
The immediate story was easy to misunderstand. On April 1-2 2026, Anthropic confirmed that a Claude Code release packaging issue was caused by human error, not a security breach. Anthropic also said no customer data or credentials were exposed. That matters. But the...