by CPI Staff | Apr 22, 2026 | Blog, Cybersecurity, Essential 8, Microsoft 365 Security, Microsoft defender XDR, Microsoft Intune
For years, Australian IT leaders treated macOS as the “quiet corner” of the fleet. A handful of executives and designers on MacBooks, a sprinkle of engineers, and a general assumption that Apple’s built-in protections were enough. That assumption no...

by CPI Staff | Apr 18, 2026 | AI Governance & Risk Management, Blog, Essential 8, Microsoft 365, Microsoft 365 Security, Microsoft Purview
Microsoft’s Deep Research in Copilot for Microsoft 365 has already reshaped how knowledge workers produce long-form analysis. Teams that used to spend days pulling together market scans, risk reviews, and competitive briefings now have a drafting partner that...

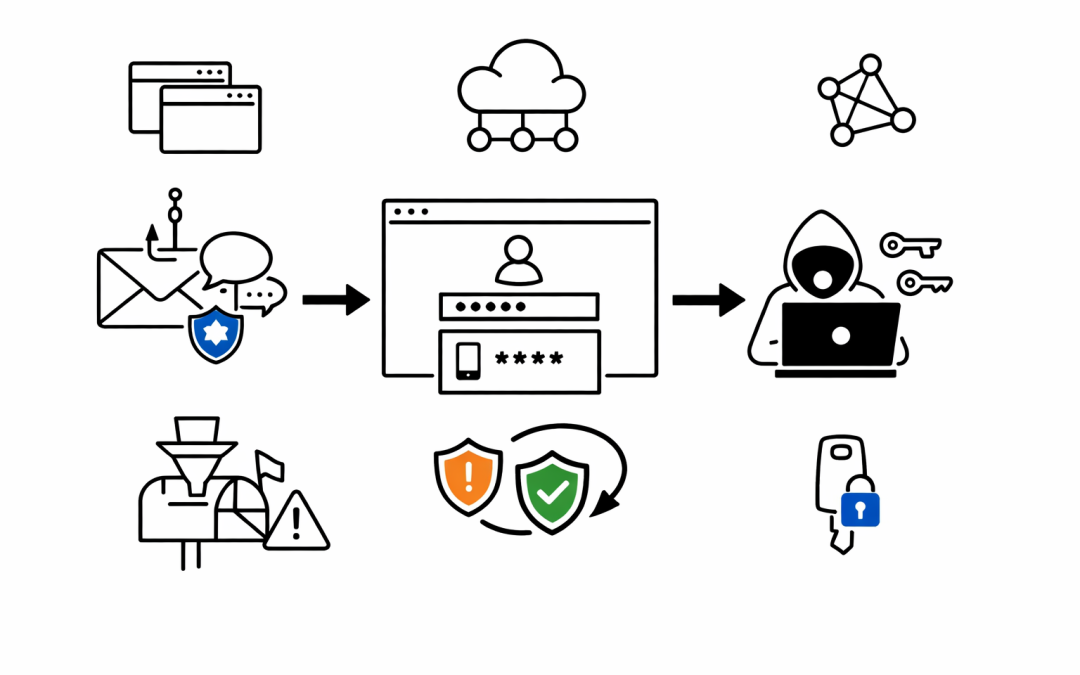
by CPI Staff | Apr 9, 2026 | AI, Blog, Cybersecurity, Entra ID, Microsoft 365 Security
Multi-factor authentication has been the security baseline for years. Most Australian organisations treat it as the final checkpoint — if MFA is in place, accounts are protected. That assumption just got a serious challenge. Microsoft Defender Security Research has...

by CPI Staff | Feb 16, 2026 | Blog, Microsoft 365 Security
In this blog post The 3 Biggest Security Gaps I See in Mid-Size Australian Businesses we will cover the most common (and fixable) security holes we see in organisations with 50–500 staff—especially those running Microsoft 365 and Azure—and what to do about them. If...

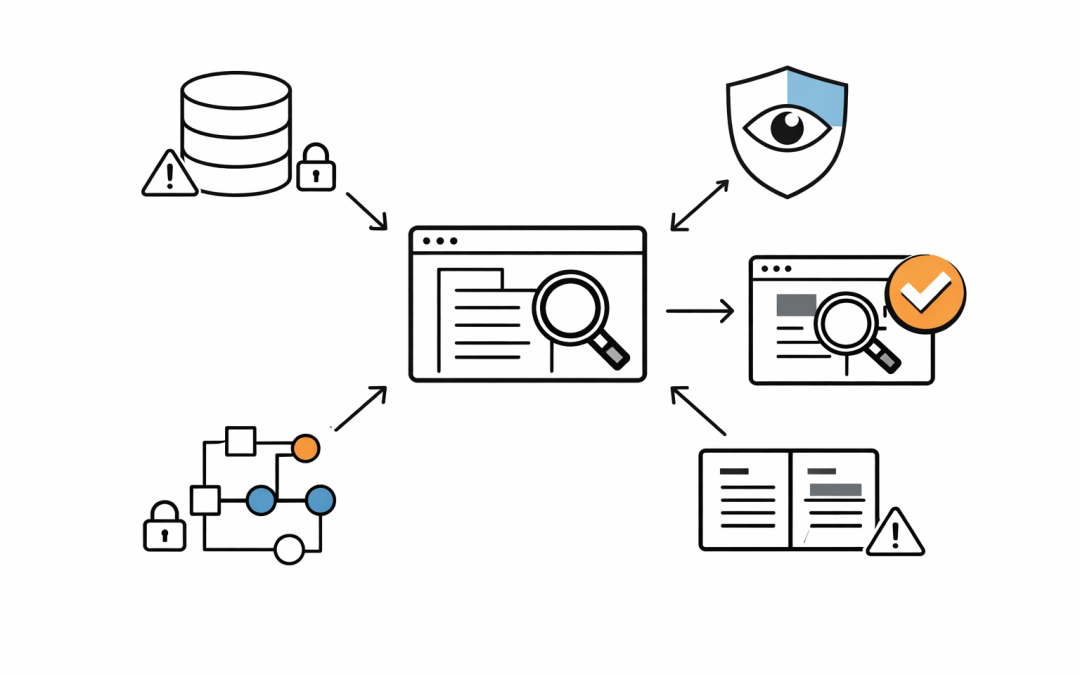
by CPI Staff | Jul 23, 2024 | Blog, Microsoft 365 Security, Microsoft defender XDR, Microsoft Graph API, Microsoft Graph security API
In this Microsoft Defender XDR article, we will show how to use Microsoft Graph Security API using a REST API client and retrieve XDR alerts. Microsoft Defender Extended Detection and Response (XDR) is an enterprise end-to-end security solution that detects, prevents,...

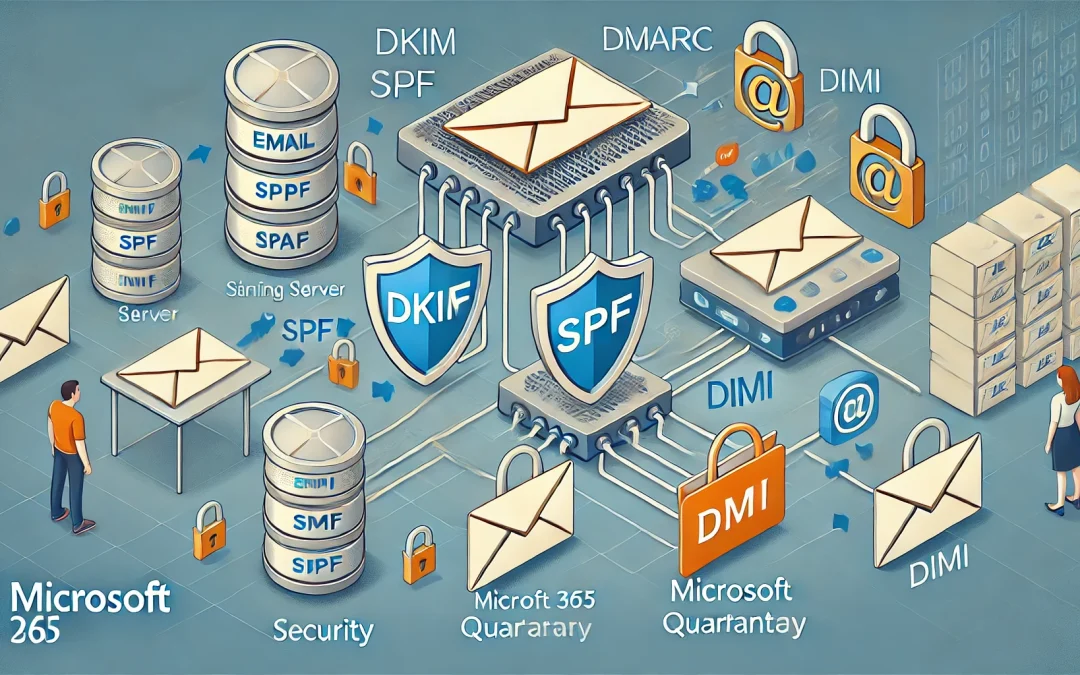
by CPI Staff | Jul 15, 2024 | Blog, Email Security, Microsoft 365, Microsoft 365 Security
In this Microsoft 365 Email Security article, we will explain how to prevent Microsoft 365 emails from blacklisting. As an IT consultancy in the Microsoft 365 space, we help Microsoft 365 customers that get affected by anti-spam systems that blacklist and graylist...