by CPI Staff | Sep 15, 2025 | Blog, Neo4j
In this blog post Create a Blank Neo4j Instance Safely on Docker, VM, or Kubernetes we will walk through how to spin up a clean, secure Neo4j deployment on Docker, a Linux VM, or Kubernetes, and why each step matters. Create a Blank Neo4j Instance Safely on Docker,...

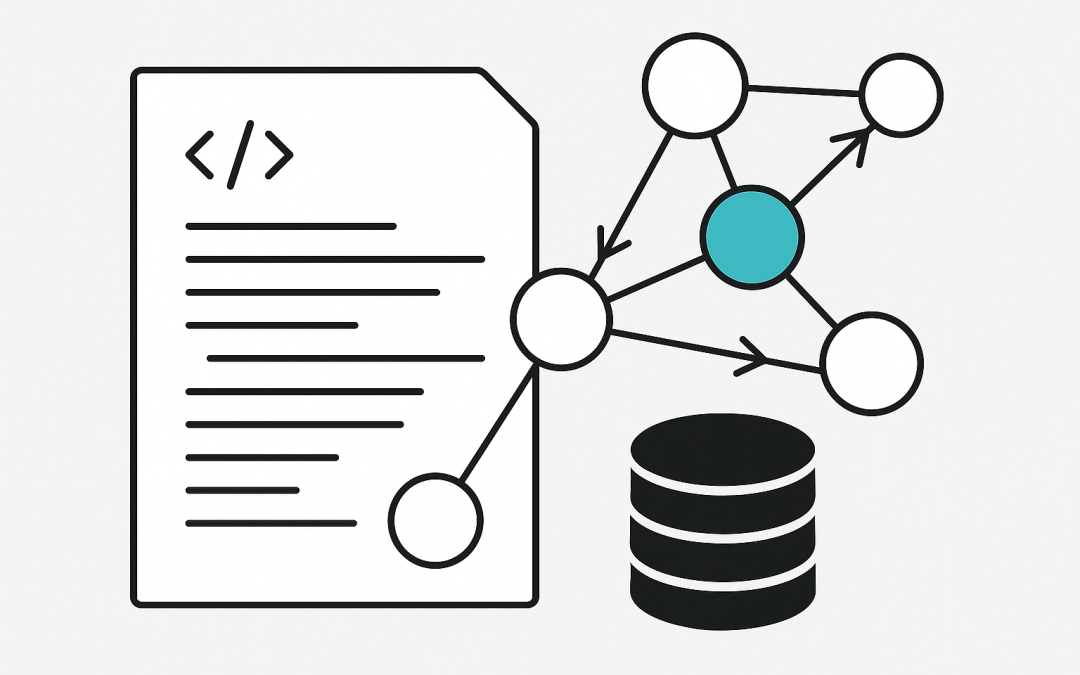
by CPI Staff | Sep 15, 2025 | AI, Blog, Neo4j
In this blog post What Are Cypher Queries and How They Power Graph Databases at Scale we will unpack what Cypher is, why it matters, and how to use it effectively. We will keep things practical, with examples and tips you can apply today. Cypher in a nutshell Cypher...

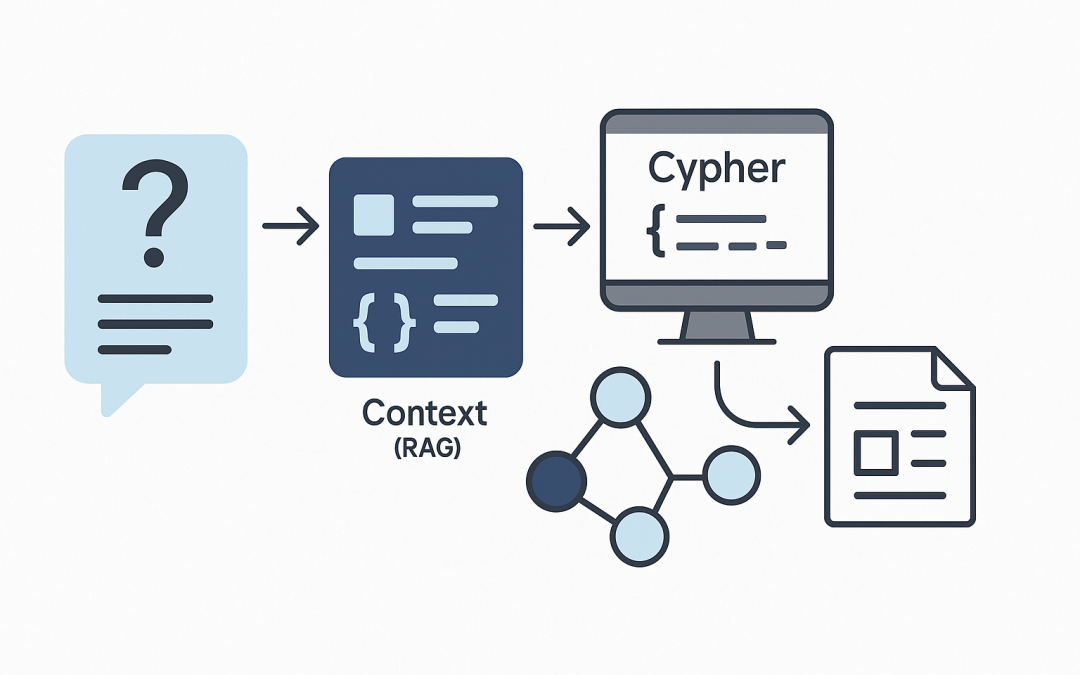
by CPI Staff | Sep 15, 2025 | AI, Blog, LLM, RAG
In this blog post Use Text2Cypher with RAG for dependable graph-based answers today we will show how to turn natural-language questions into precise Cypher queries and reliable answers over your graph data. Before diving into code, let’s clarify the idea. Text2Cypher...

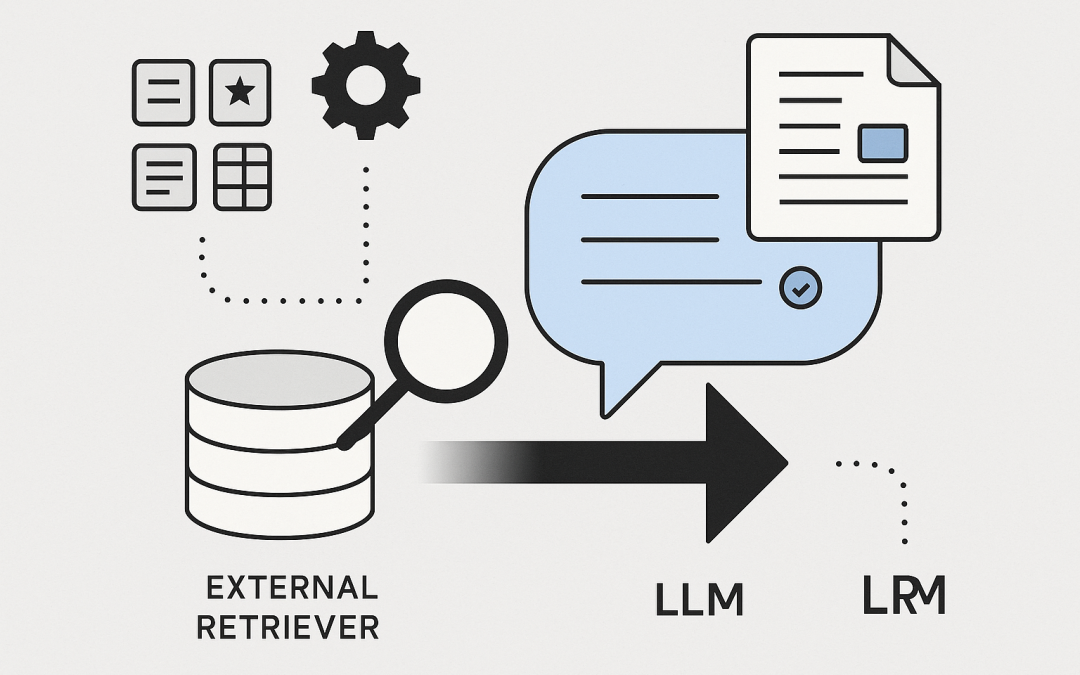
by CPI Staff | Sep 15, 2025 | Blog, LLM, RAG
In this blog post Architecture of RAG Building Reliable Retrieval Augmented AI we will unpack how Retrieval Augmented Generation works, what to build first, and how to run it reliably in production. Retrieval Augmented Generation (RAG) combines a large language model...

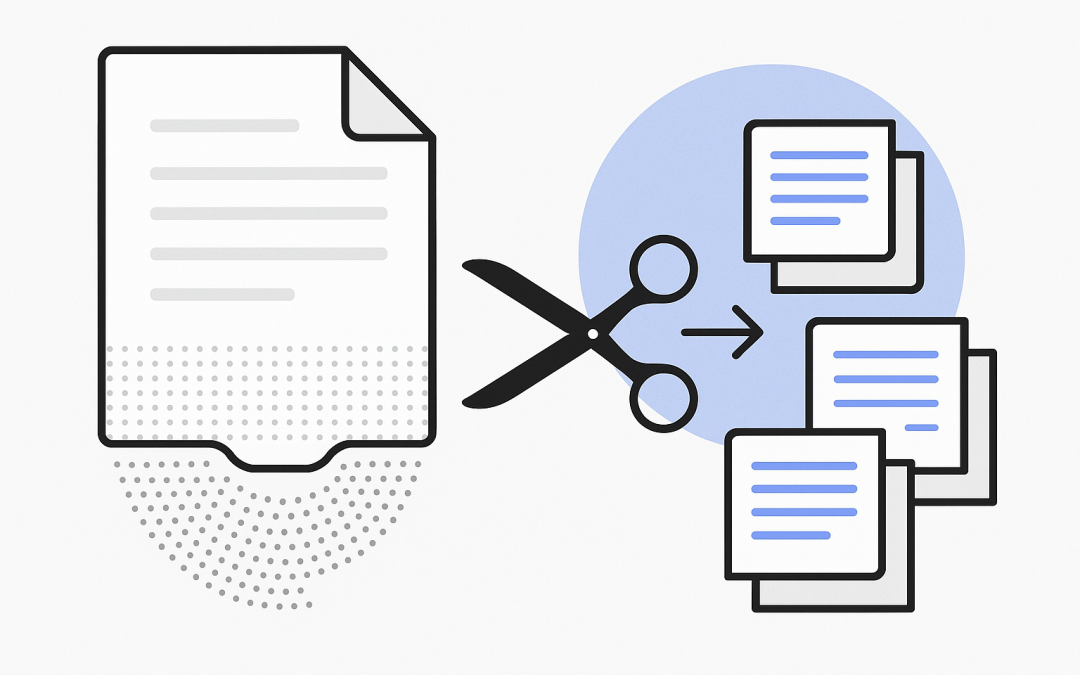
by CPI Staff | Sep 15, 2025 | Blog, RAG
In this blog post How Text Chunking Works for RAG Pipelines and Search Quality we will unpack what text chunking is, why it matters, and how to do it well in real systems. Text chunking is the practice of splitting large documents into smaller, coherent pieces so...

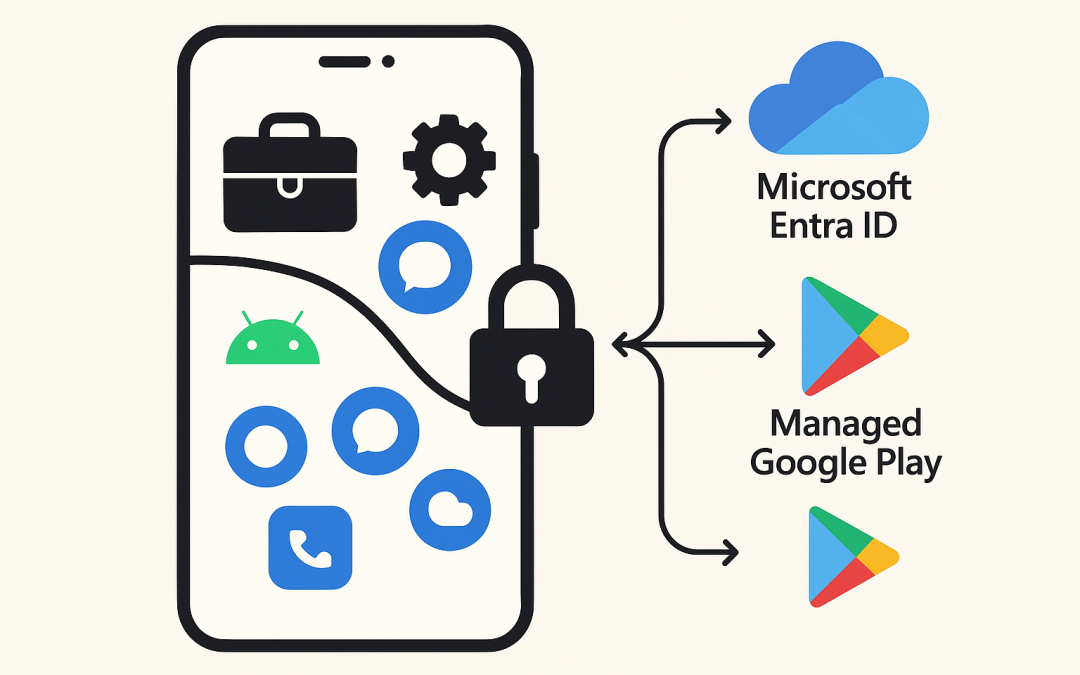
by CPI Staff | Sep 15, 2025 | Blog, Microsoft Intune
In this blog post Manage Android BYOD with Microsoft Intune using Work Profile we will show how to protect company data on personal Android devices without taking over the whole phone. We’ll balance user privacy with strong security controls and give you practical...