Most organisations still treat dependency management as a developer hygiene issue. The Axios npm compromise shows that assumption is now dangerous.
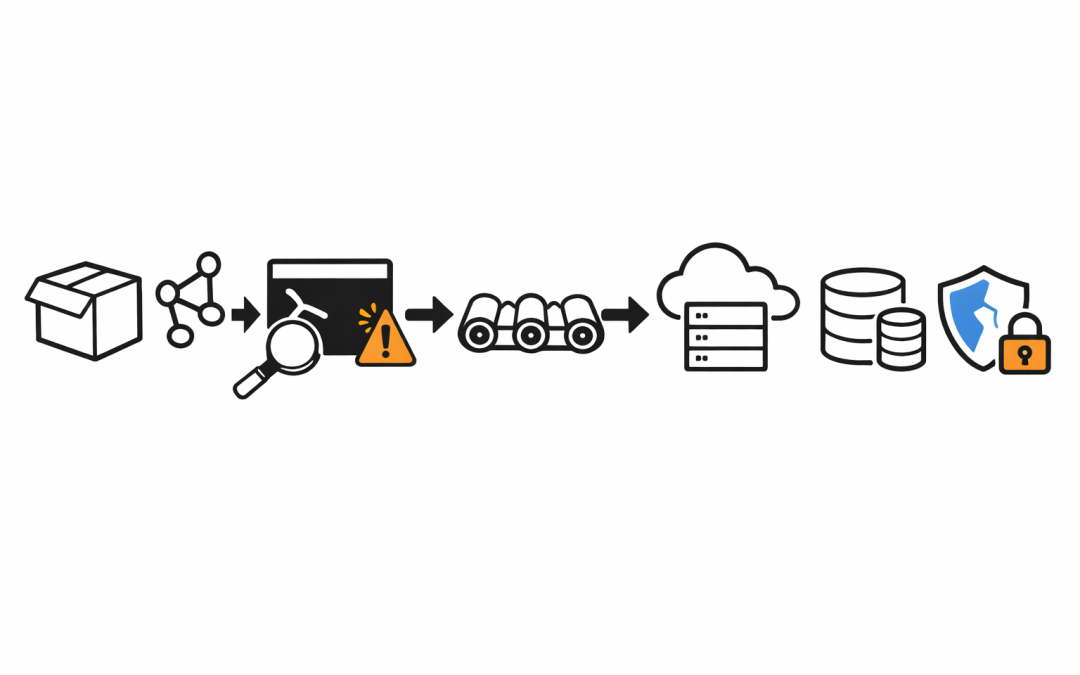
When two malicious Axios versions were published on March 31, 2026, the problem was not limited to a bad package update. According to Microsoft Threat Intelligence, axios@1.14.1 and axios@0.30.4 pulled in a malicious dependency, plain-crypto-js@4.2.1, which executed during installation, connected to attacker infrastructure, and downloaded second-stage payloads for Windows, macOS, and Linux. For any organisation that allows routine auto-updates in developer environments or CI/CD pipelines, that turns a standard package refresh into a remote access event.
For mid-market Australian organisations, this is the real lesson: dependency governance has become an enterprise risk issue, not a narrow software engineering concern.
The Attack Worked Because Trust Was Assumed
The most concerning part of this incident is how little had to change for the compromise to work. Microsoft reported that the Axios source code itself was not materially altered. Instead, the malicious versions added a runtime dependency with an install-time hook, so the compromise triggered when npm resolved and installed the package.
That matters because many internal controls focus on application behaviour after deployment. This attack shifted the compromise earlier into the software supply chain, at the point where developer workstations and build systems routinely trust package managers to fetch and execute what they need.
In practical terms, a normal npm install or npm update could initiate outbound traffic to attacker-controlled infrastructure and deploy a remote access trojan without breaking the application. That is exactly the kind of activity many teams are least prepared to detect, because the package installation still appears to “work.”
Why Dependency Governance Failed
The Axios incident exposed four governance gaps that are common across mid-market environments.
Version ranges created hidden exposure. Many teams still use caret or tilde versioning for convenience. That means a dependency can move to a newly published minor or patch release without a deliberate security review. In this case, Microsoft warned that projects permitting versions beyond safe Axios releases could retrieve the malicious package automatically.
Build pipelines were treated as trusted by default. CI/CD systems often have privileged access to source control, package registries, secrets stores, cloud credentials, and deployment targets. Once a poisoned package executes during build or install, the blast radius can extend well beyond a developer laptop.
Install-time script execution was not tightly controlled. The malicious plain-crypto-js package used npm lifecycle behaviour to launch its loader. Many organisations still allow postinstall scripts broadly because parts of the JavaScript ecosystem depend on them. That may be operationally convenient, but it is also a clear attack path.
Security monitoring was not aligned to package management risk. Traditional endpoint and network controls are often tuned for phishing, malware downloads, or suspicious binaries, not for malicious behaviour triggered by legitimate package installation activity inside developer or build environments.
This Is a Board-Level Issue When Development Environments Hold Privileged Access
The business risk is larger than a compromised JavaScript dependency. Modern delivery pipelines are connected to systems that matter to the whole organisation: cloud environments, production workloads, signing infrastructure, internal repositories, and customer-facing applications.
If an attacker gains remote access through a developer endpoint or build runner, the question is no longer “Was Axios affected?” The real question becomes “What secrets, systems, and deployment paths were reachable from the compromised environment?”
That is why this belongs in enterprise risk and governance discussions. Dependency events can now create operational disruption, data exposure, service integrity issues, and regulatory consequences. For Australian organisations dealing with privacy obligations, cyber insurance requirements, and board scrutiny over software supply chain resilience, this cannot stay buried inside engineering backlogs.
What Australian Organisations Should Do Now
Microsoft’s immediate guidance was clear: roll back to safe Axios versions, check for axios@1.14.1, axios@0.30.4, and plain-crypto-js@4.2.1, rotate exposed secrets, review build logs, and investigate connections to sfrclak[.]com or 142.11.206[.]73 on port 8000.
That is the urgent response. The longer-term fix is governance.
Pin critical dependencies exactly. For high-risk packages that sit deep in application stacks, remove automatic version drift. Exact pinning will slow some update workflows, but it materially reduces exposure during supply chain events.
Use overrides for transitive control. If a package arrives indirectly, teams still need a way to force safe versions across the dependency graph. This should be a standard operating pattern, not an emergency response improvisation.
Restrict lifecycle scripts where possible. If a build does not require install scripts, disable them. Where they are necessary, isolate those builds, reduce privileges, and monitor them more aggressively.
Reassess CI/CD trust boundaries. Build systems should not have broad standing access to everything needed for delivery. Segment secrets, use short-lived credentials, and minimise what a compromised runner can reach.
Adopt trusted publishing practices. Microsoft highlighted the value of Trusted Publishing with OIDC to reduce reliance on stored credentials. That does not solve every supply chain problem, but it does remove one common route for malicious releases.
Tune detection to package-install behaviour. Security teams should treat anomalous install-time activity, unexpected outbound connections from build systems, and postinstall execution patterns as first-class signals.
The Essential 8 Conversation Needs to Extend Into Software Supply Chains
The ACSC Essential 8 was not written specifically for npm compromises, but several controls map directly to the weaknesses this incident exposed.
Application control matters when install-time scripts and unexpected payloads attempt execution. Restricting administrative privileges matters when developer endpoints and runners can pivot into higher-value systems. Patch management still matters, but this incident is a reminder that “staying current” without governance can itself become a source of risk.
For organisations that have invested in Essential 8 uplift, the next step is to test whether those controls meaningfully cover developer tooling, package installation flows, and CI/CD infrastructure. In many environments, they do not.
The Real Governance Question
The Axios compromise was serious because it exploited a trusted distribution path used at enormous scale. But the bigger issue is structural: too many organisations still have no formal policy for which dependencies can auto-update, which build environments can execute install scripts, and how package-origin anomalies are investigated.
That is a governance failure, not just a tooling gap.
Organisations that respond by downgrading Axios and moving on will likely face the same problem again under a different package name. Organisations that use this moment to tighten dependency controls, reduce CI/CD privilege, and improve software supply chain monitoring will be in a much stronger position for the next incident.
Our team works with Australian organisations to strengthen cloud, AI, and cybersecurity governance across delivery pipelines, endpoint controls, and software supply chains. If this incident exposed uncertainty around how much trust your build and dependency ecosystem currently assumes, that is a useful place to start the next security review.
CloudProInc is a Microsoft Partner and Wiz Security Integrator, working with Australian organisations on cloud, AI, and cybersecurity strategy. follow us on LinkedIn